AI · Analytics · LLM Inference
The Encryption-in-use platform for software teams working with sensitive data.
Ship the projects that stalled at legal review. Queries return in under a second — and we never see plaintext.
SOC 2 Type 2 · HIPAA · GDPR · FIPS 140-3 · AES-GCM-256 · NIST-validated
Production speed on encrypted data.
Benchmarked on our internal test clusters against 100K–1M encrypted records.
The encrypted data platform
Sensitive data.
Back on the table.
Real-time searchable encryption
=, <, >, sum, avg, count, min, max, fuzzy match. Every operation runs on encrypted fields, at millisecond latency across millions of records.
Your database answers questions about data it never decrypts. Ranges, aggregates, fuzzy matches — executed on ciphertext, accurate to plaintext, in under a second.
blind record list --schema UDarTJg3K6 \
--filter "risk_level:count(50~100)" \
--filter "account_jurisdiction:JP"
# → 247 (aggregate only — no records returned)Fine-grained access controls
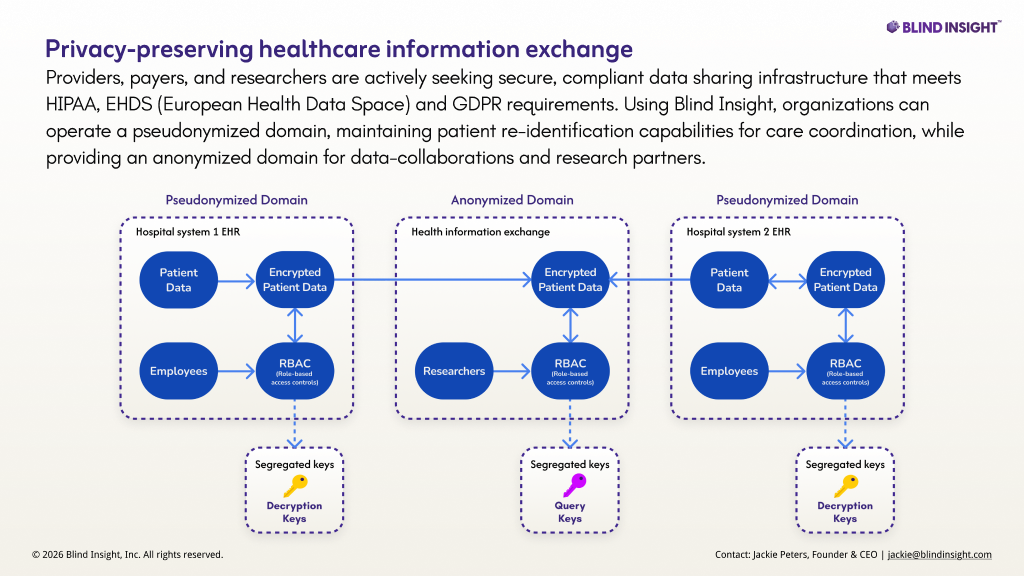
Field-level grants by identity, checked on every query and every decrypt. Proxy-backed key segregation keeps cross-border data in its jurisdiction.
blind grants create --data '{
"name": "analyst-read",
"field_names": {"risk_level": true, "account_id": false},
"can_create_records": false
}'Audit-ready logs and monitoring
An immutable, cryptographically signed audit trail of every query, grant, and decrypt — exportable to your compliance stack without a follow-up ticket.
Real-time searchable encryption
=, <, >, sum, avg, count, min, max, fuzzy match. Every operation runs on encrypted fields, at millisecond latency across millions of records.
Fine-grained access controls
Field-level grants by identity, checked on every query and every decrypt. Proxy-backed key segregation keeps cross-border data in its jurisdiction.
Audit-ready logs and monitoring
An immutable, cryptographically signed audit trail of every query, grant, and decrypt — exportable to your compliance stack without a follow-up ticket.
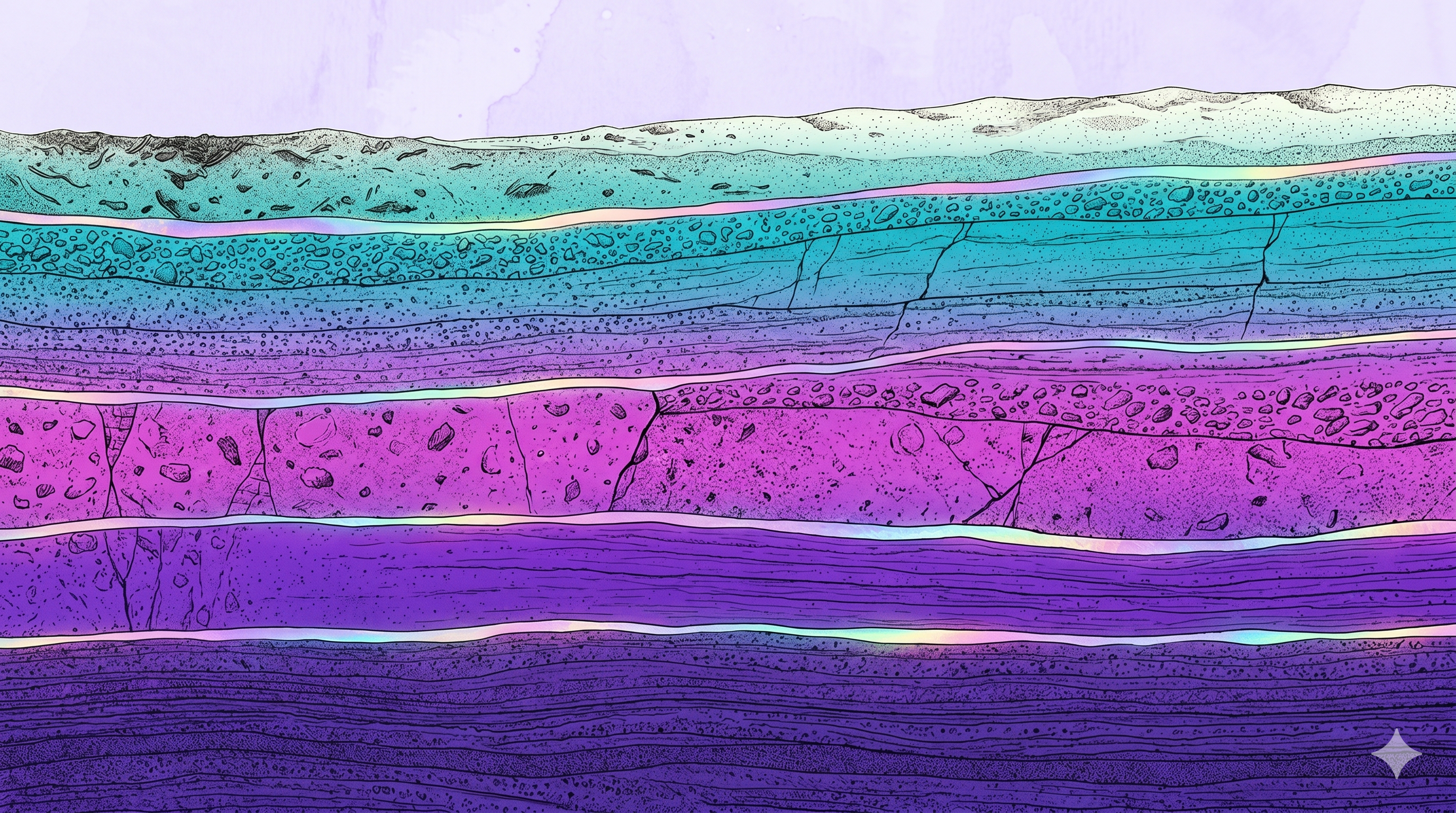
The query layer
How a query crosses the boundary without crossing the line.
Blind(L)LM™
Let any LLM operate on encrypted data.
Translates prompts into encrypted queries or BlindML model runs, assigns the minimum key set an agent needs, and revokes access at session end. The model never sees a raw customer record.
from blind_llm import BlindInsightOrchestrator
orc = BlindInsightOrchestrator(backend=proxy_backend)
r = orc.run("Cancer rate for women 60+ with dense breast tissue?")
# LLM sees only aggregate counts — no raw records
print(r.answer)BlindML
scikit-learn for encrypted data.
Naive Bayes, decision trees, logistic regression—trained on aggregate counts from encrypted data. Bring your own scikit-learn model. 0.0 F1 delta vs. plaintext baseline on 600K records.
from blind_ml import NaiveBayesModel
model = NaiveBayesModel().fit(marginals, n_pos=3201, n_neg=76402)
pred, risk = model.predict({"fraud_type": "card_fraud"})
# 0.0 F1 delta vs. plaintext — 600K recordsThe numbers.
- Sublinear scaling
- 2× data, <2× latency
- 0.7× storage footprint
- No plaintext shadow
- SOC 2 Type 2
- Compliant
- HIPAA
- k=11 suppression built in
- FIPS 140-3
- AES-GCM-256 · NIST-validated
“I put Blind Insight on the roadmap because it’s the first time I’ve seen query performance on encrypted data that’s actually usable in production. The approach is spot-on.”
Start on your schema. 72 hours. Nothing to deploy.
Get started at the Build tier, $9/month.