Use cases
Proof, not promises.
Production deployments of searchable encryption across regulated industries. Real workloads, measured outcomes.
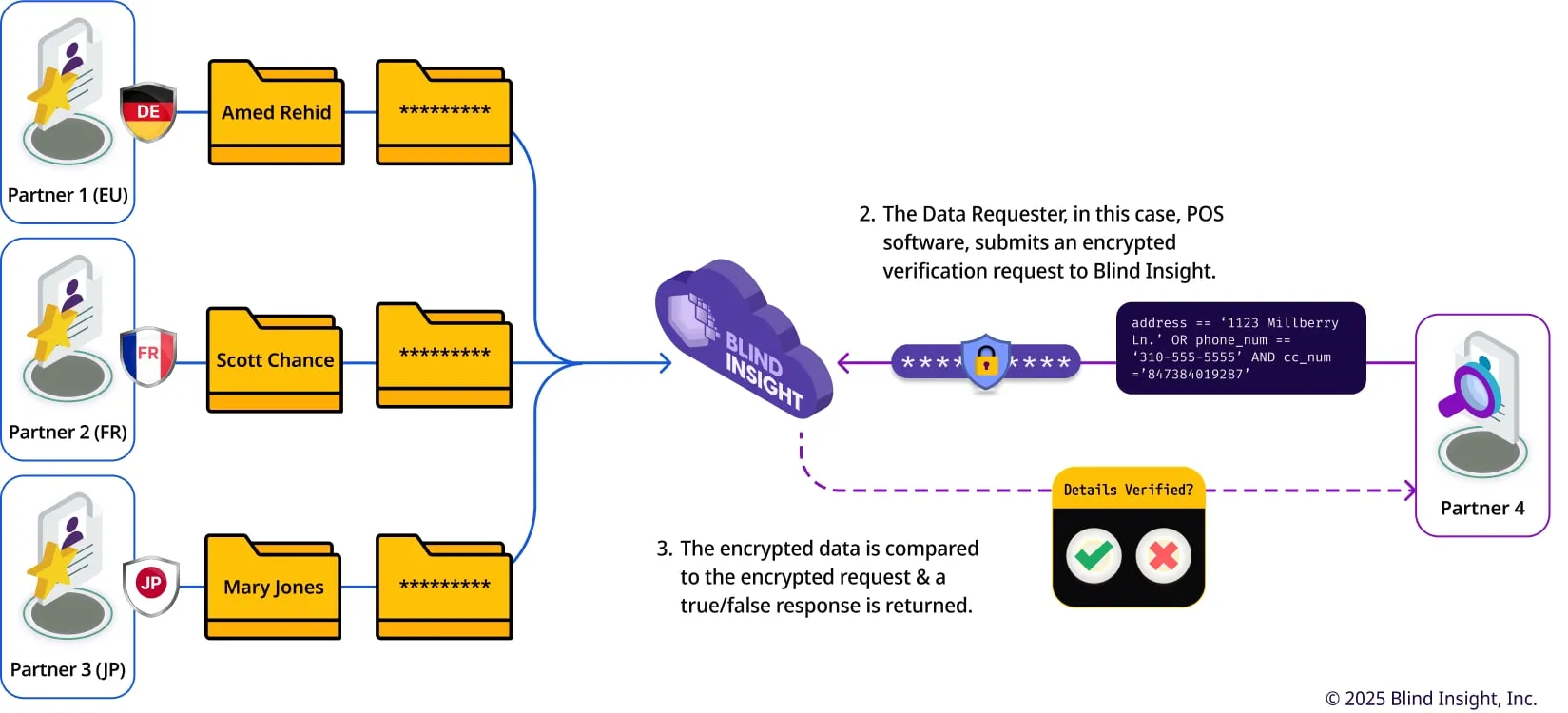
Financial services
GDPR-Compliant Crossborder Fraud Prevention
Global privacy regulations have made it harder than ever to mobilize crucial data used in fraud prevention. Using Blind Insight, data is encrypted by the original Data Owner in their environment.
Read case →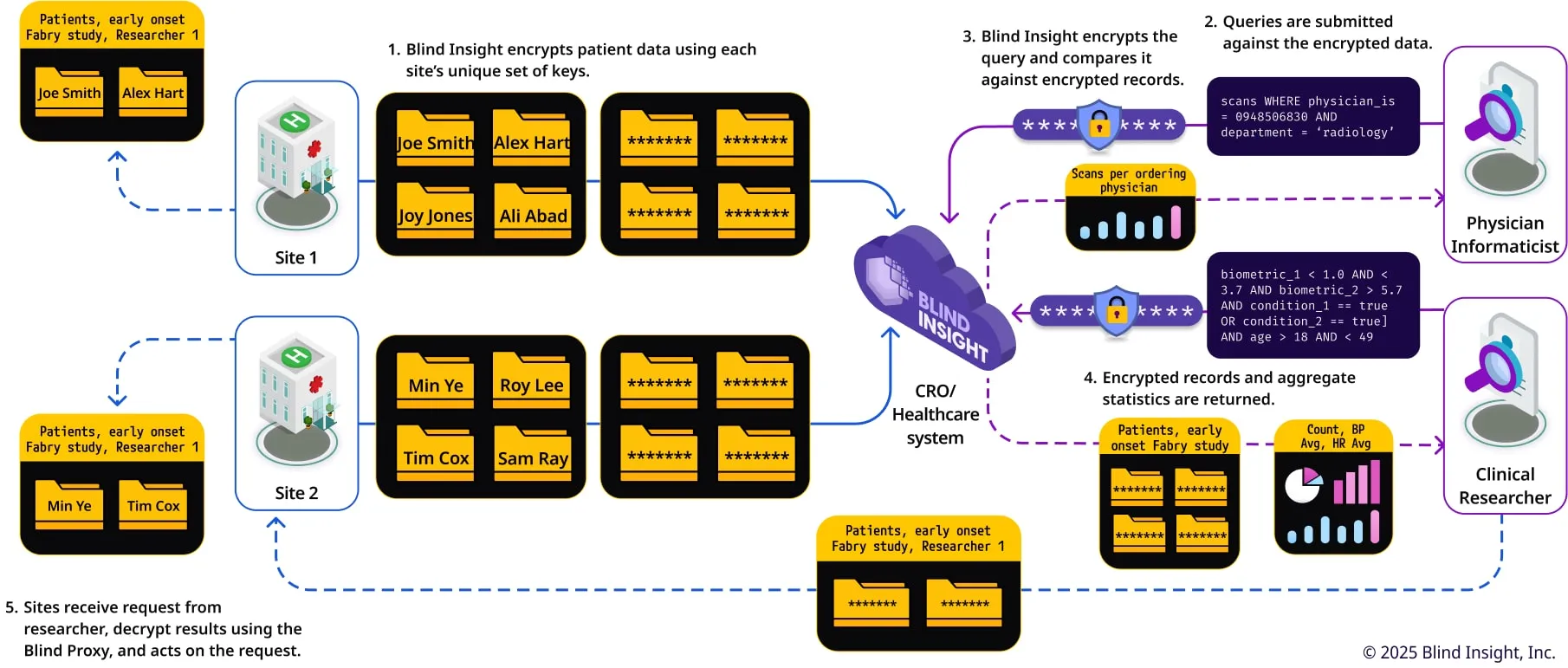
Healthcare
A privacy-preserving health information exchange
Use Blind Insight to increase operational efficiency, identify and recruit participants, incorporate real-world-evidence, or run post-marketing trials while remaining compliant and secure.
Read case →
SaaS vendors
A Privacy-Preserving Customer Service Center
Learn how Blind Insight can be used in customer support workflows.
Read case →